 Microsoft Azure Network Security Group (NSG)
Microsoft Azure Network Security Group (NSG)
When you are implementing your Microsoft Azure Design like a HUB-Spoke model you have to deal with security of your Azure environment (Virtual Datacenter). One of them are Network Security Groups to protect your Virtual networks and make communication between Azure subnets possible in a Secure Azure Virtual Datacenter.
You really have to plan your Azure Virtual networks and implement it by Architectural Design. Now I’m writing about Azure Network Security Groups which is important, but there are more items to deal with like :
- Naming Conventions in your Azure Virtual Datacenter
- Azure Subscriptions ( who is Owner, Contributor, or Reader? )
- Azure Regions ( Where is my Datacenter in the world? )
- Azure VNET and Sub-Nets ( IP-addresses )
- Security of your Virtual Networks ( Traffic filtering, Routing )
- Azure Connectivity ( VNET Peering between Azure Subscriptions, VPN Gateway )
- Permissions (RBAC)
- Azure Policy ( Working with Blue prints )
Here you can read more about these Microsoft Azure items
How to Manage Microsoft Azure Network Security Groups (NSG) ?
IMPORTANT: Before you start with Azure Network Security Groups, test every ARM JSON Script first in your Dev-Test Azure Subscription before you do production. Talk with your Cloud Administrators, because when you implement Infrastructure as Code (IaC) and work with ARM Templates you can delete manual settings in NSG’s for example, which will give you troubles like no protocol communication between subnets.
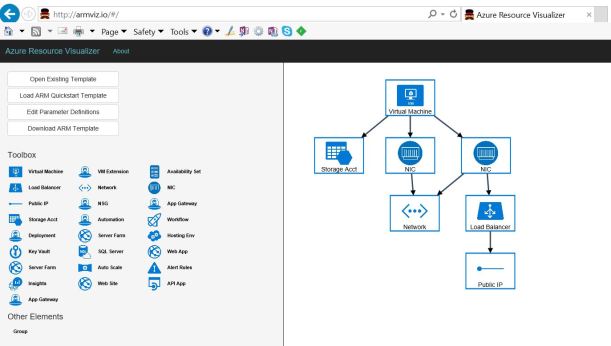
When you start new in Microsoft Azure, It’s easy to make your Azure security baseline for all of your Network Security Groups (NSG’s) by Azure Resource Manager (ARM) templates.
When you have a Microsoft Azure HUB-Spoke model with for example four Azure Subscriptions and a lot of Azure Virtual Networks – Subnets, you got a lot of NSG’s to manage and you don’t want to manage those manually. So there are different ways to manage Azure Network Security Groups via ARM Templates. For example :
 ARM Templates from the Azure Portal
ARM Templates from the Azure Portal
 Make your ARM Baseline template.
Make your ARM Baseline template.
 Edit your parameters and Deploy.
Edit your parameters and Deploy.
Here you saw a standard Virtual Machine Deployment, but you can add of course all of your Azure Resource Manager templates here including your NSG Base Line template. In this way your deployments are documented ( Scripts).
Another awesome solution is Microsoft Azure DevOps for your Deployments in Azure.
Azure DevOps Services is a cloud service for collaborating on code development. It provides an integrated set of features that you access through your web browser or IDE client. The features are included, as follows:
- Git repositories for source control of your code
- Build and release services to support continuous integration and delivery of your apps
- Agile tools to support planning and tracking your work, code defects, and issues using Kanban and Scrum methods
- Many tools to test your apps, including manual/exploratory testing, load testing, and continuous testing
- Highly customizable dashboards for sharing progress and trends
- Built-in wiki for sharing information with your team
The Azure DevOps ecosystem also provides support for adding extensions and integrating with other popular services, such as: Campfire, Slack, Trello, UserVoice, and more, and developing your own custom extensions.
Choose Azure DevOps Services when you want the following results:
- Quick set up
- Maintenance-free operations
- Easy collaboration across domains
- Elastic scale
- Rock-solid security
You’ll also have access to cloud load testing, cloud build servers, and application insights.
Azure DevOps Repo for your Templates
From here you can make your Infrastructure as Code (IaC) Pipelines together with your Cloud Administrator Team 😉
When you have your Azure DevOps Private Repository in place and you like to work with Visual Studio for example, you can connect to your Repo and Check-in your NSG ARM Script but Deploy with Visual Studio to your Azure Virtual Datacenter.
 Azure NSG Template Deployment via Visual Studio
Azure NSG Template Deployment via Visual Studio
Microsoft Visual Studio 2019 Preview is available for download here
Here you can download Microsoft Visual Studio Community Edition
And there is Microsoft Open Source Visual Studio Code
 Azure DevOps Repo in Visual Studio Code.
Azure DevOps Repo in Visual Studio Code.
Microsoft Visual Studio Code work with Extensions :
Azure DevOps Pipelines Extension
So you see there are enough ways to deploy ARM Templates and this is not all, because you can also use Azure Cloudshell for example or other CLI command-line interfaces. But now we want to set the NSG Baseline for our Azure Subscription. A good start is to see the possibilities in the JSON scripting for Network Security Groups.
Here you find the settings and explanation of Azure Components.
For Microsoft Azure NSG Template :
Azure NSG Baseline Template
To create a Microsoft.Network/networkSecurityGroups resource, add the following JSON to the resources section of your template.
The Microsoft Azure Quick Create Templates on Github can help you to make your own NSG Template for example.
————————————————————————–
“apiVersion”: “2017-06-01”,
“type”: “Microsoft.Network/networkSecurityGroups”,
“name”: “[parameters(‘parkingzoneNSGName’)]”,
“location”: “[parameters(‘location’)]”,
“properties”: {
“securityRules”: [
/* {
“name”: “Allow_RDP_Internet”,
“properties”: {
“description”: “Allow RDP”,
“protocol”: “Tcp”,
“sourcePortRange”: “*”,
“destinationPortRange”: “3389”,
“sourceAddressPrefix”: “Internet”,
“destinationAddressPrefix”: “*”,
“access”: “Allow”,
“priority”: 500,
“direction”: “Inbound”
}, */
{
“name”: “AllowAzureCloudWestEuropeOutBound”,
“properties”: {
“protocol”: “*”,
“sourcePortRange”: “*”,
“destinationPortRange”: “*”,
“sourceAddressPrefix”: “*”,
“destinationAddressPrefix”: “AzureCloud.WestEurope”,
“access”: “Allow”,
“priority”: 999,
“direction”: “Outbound”
}
},
{
“name”: “DenyInternetOutBound”,
“properties”: {
“protocol”: “*”,
“sourcePortRange”: “*”,
“destinationPortRange”: “*”,
“sourceAddressPrefix”: “*”,
“destinationAddressPrefix”: “Internet”,
“access”: “Deny”,
“priority”: 2000,
“direction”: “Outbound”
}
}
]
}
},
————————————————————–
By Default is Internet available in a NSG ! So here you see that Internet is not allowed only the AzureCloud West Europe resources because some Azure SDK Component work via ” Public internet” ( Microsoft IP-Addresses).
(RDP protocol is marked and not set in this example for Security reasons)
 Internet by Default Rules, so you must set your security Rules !
Internet by Default Rules, so you must set your security Rules !
Conclusion :
You really have to implement Azure Security by Design, make your Base-line with ARM Templates in a Private Repo for your Azure Network Security Groups with the Correct RBAC Configuration for your Cloud Administrator Team. Don’t make them manually and do settings manually when you have a lot of NSG’s ! Versions of your ARM templates are documented in your Repository 😉
Test Always first in a Dev-Test Azure Subscription or in Azure DevOps with a Test plan before you implement in Production.



































 Here you can find Up-to-Date
Here you can find Up-to-Date